✓
Shield Cyber
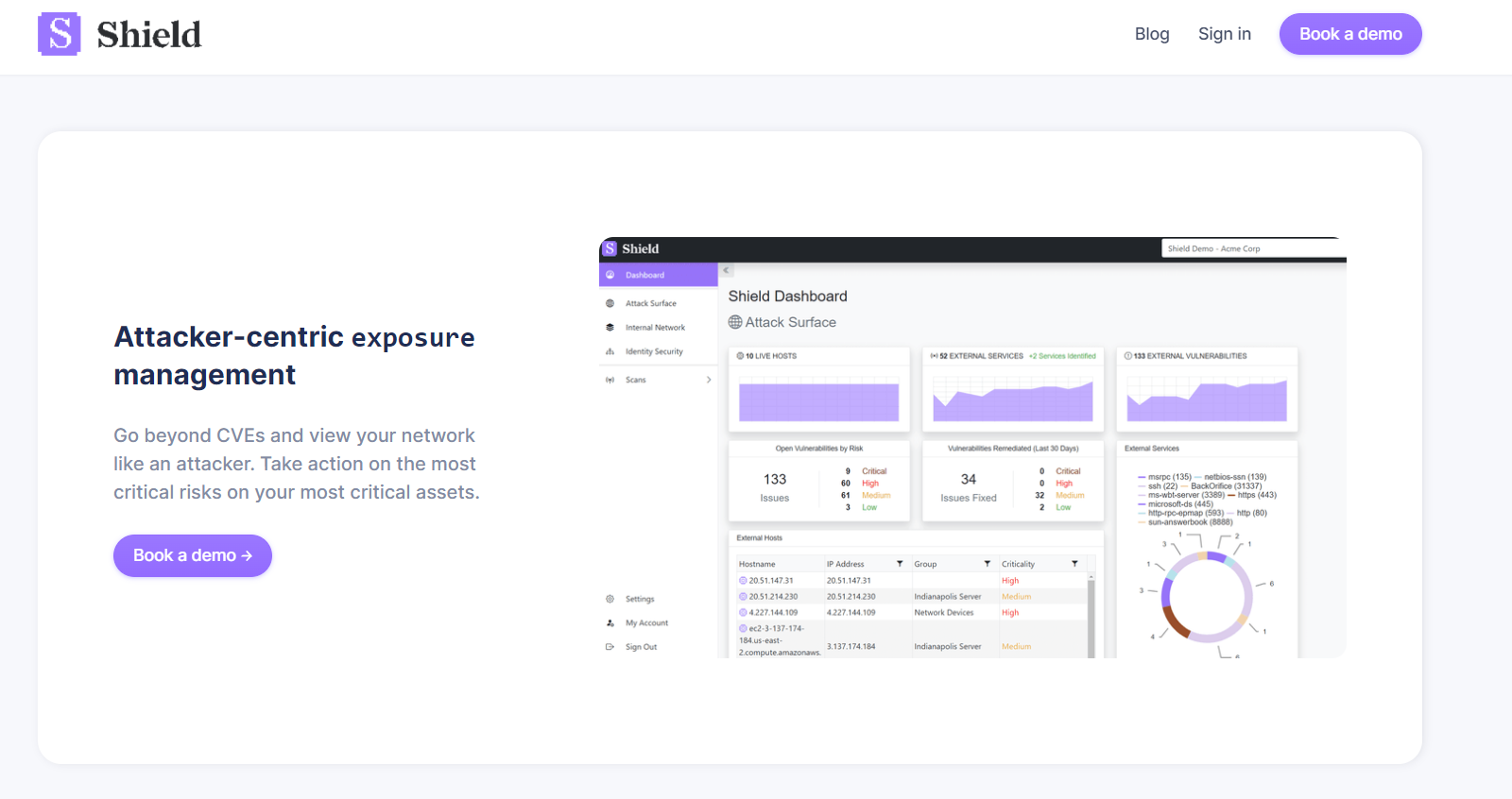
Shield continuously detects cyber risks across an organization's entire attack surface. Developed by penetration testers. Designed for the IT channel.
Shield is an identity-based and real-time vulnerability management platform.
Shield’s custom tooling allows risks to be continuously evaluated across the entire attack surface, including external attack surface management, internal vulnerability management, and Active Directory (identity) security.
Built by penetration testers, Shield is designed to detect and prioritize exposures from the perspective of an attacker – not some theoretical risk score.
This allows for true prioritization of risk based on each individual network makeup, automated and displayed in a dynamic dashboard, with clear next steps to remediation.
In simple terms, Shield distinguishes the critical few from the trivial many, giving managed security providers back control.