Table of contents
mitmproxy
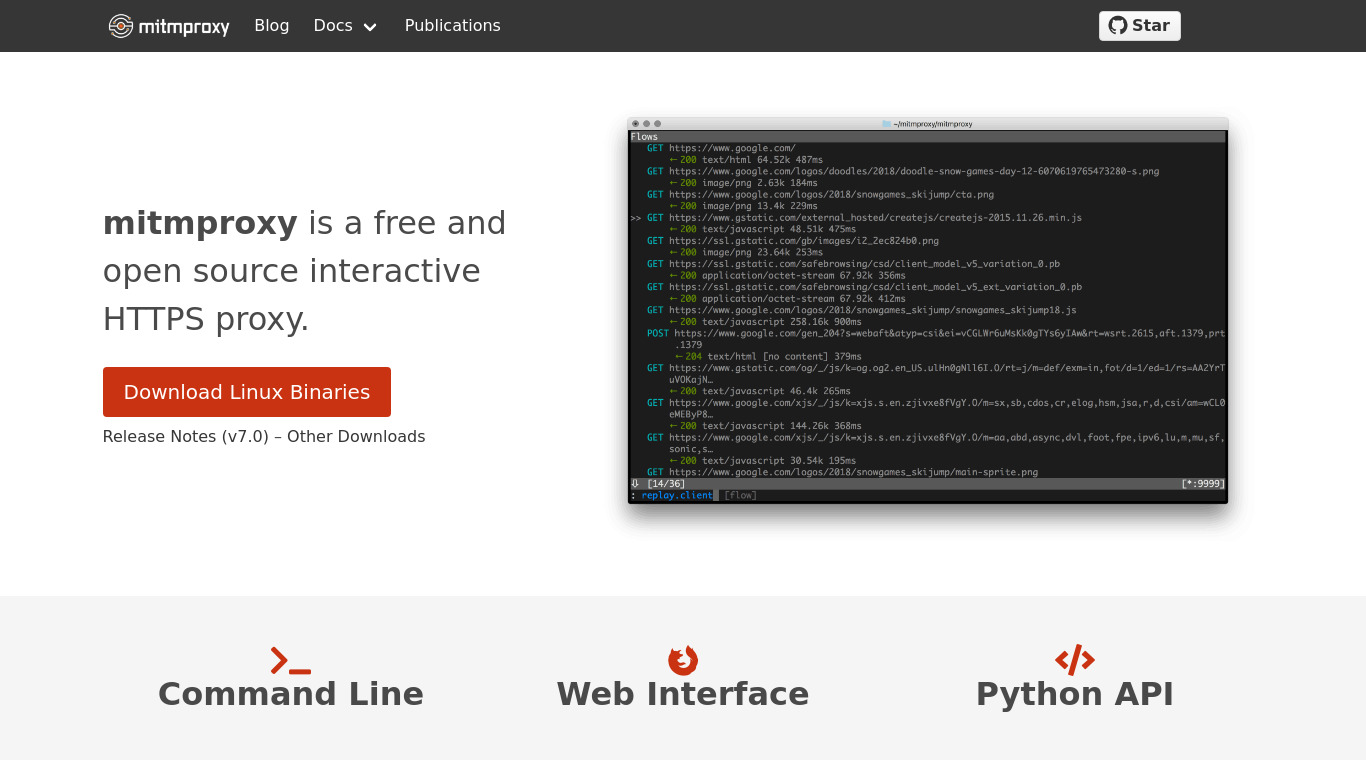
mitmproxy is an SSL-capable man-in-the-middle proxy for HTTP. subtitle
As mitmproxy is an open source project, you can find more
open source alternatives and stats
on LibHunt.
Pricing:
- Open Source