Panda Security
Panda Security is an antivirus and cyber security solution. subtitle
Panda Security Alternatives [Page 8]
The best Panda Security alternatives based on verified products, community votes, reviews and other factors.
Latest update:
-
/moon-secure-alternatives
Download Moon Secure Antivirus for free.
-
/screenview-alternatives
Endpoint Management
-
Try for free
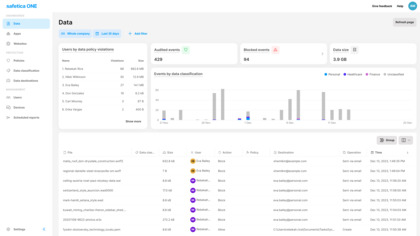
We believe data protection should make running your business easier, not harder. Safetica protects companies against insider threats, offers data loss protection, and supports regulatory compliance.
-
/seculution-application-whitelisting-alternatives
No more malware. Guaranteed! seculution's antivirus solution is based on application whitelisting, malware that is not known cannot be executed.
-
/ultra-file-search-alternatives
Ultra File Search is a Search Utility which is able to quickly find Files, Folders and Text on your Local, Network, DVD, CD-ROM, USB Hard or Flash Drives.
-
/cyamast-alternatives
CyAmast is a cybersecurity software that gives you the visibility and analytics to protect your governmental desktop, mobile, tablet, and IoT connected devices.
-
/votiro-disarmer-for-removable-devices-alternatives
Votiro Disarmer for removable devices ensures proper endpoint device control and eliminates this high risk by detecting and scanning every plugged-in device
-
/manageengine-patch-manager-plus-alternatives
Patch Manager Plus, an all-round patching solution, offers automated patch deployment for Windows, macOS, and Linux endpoints, plus patching support for 350+ third-party applications You can use it to patch computers within LAN and WAN.
-
/cisco-alternatives
Cisco is the worldwide leader in IT, networking, and cybersecurity solutions. We help companies of all sizes transform how people connect, communicate, and collaborate.
-
/userlock-alternatives
Secure Active Directory user logins with two factor authentication, single sign-on, contextual access controls and real-time monitoring and reporting.
-
/bufferzone-alternatives
For years, the most secure facilities have used the concept of a buffer zone to isolate sensitive operations and information.
-
/intuit-data-protect-for-quickbooks-alternatives
Secure online backup of your critical business data
-
/stormshield-endpoint-protection-alternatives
Stormshield Endpoint Security: a proactive response to modern threats, protection for workstations, servers and terminal devices
-
/observable-networks-alternatives
Cisco Stealthwatch Cloud provides behavioral analytics across your network to help you identify advanced threats faster and achieve a stronger security posture.