Google Cloud IAM
Google Cloud Identity & Access Management (IAM) lets administrators authorize who can take action on specific resources, giving you full control and visibility to manage cloud resources centrally. subtitle
Google Cloud IAM Alternatives [Page 5]
The best Google Cloud IAM alternatives based on verified products, community votes, reviews and other factors.
-
/grpc-alternatives
Application and Data, Languages & Frameworks, Remote Procedure Call (RPC), and Service Discovery
-
/ca-identity-management-alternatives
Identity Management solutions help increase user productivity and business flexibility with user provisioning and identity governance.
-
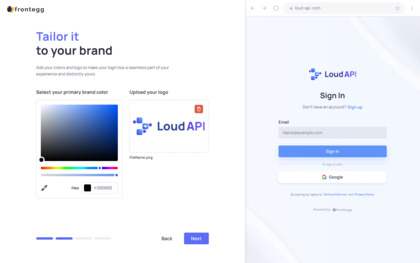
Try for free
Elegant user management, tailor-made for B2B SaaS
-
/sap-grc-alternatives
SAP solutions for governance, risk, and compliance (GRC) help companies minimize risk and stay in compliance with regulations.
-
/cas-alternatives
Apereo CAS - Enterprise Single Sign On for the Web
-
/lastpass-alternatives
LastPass is an online password manager and form filler that makes web browsing easier and more secure.
-
/google-automl-tables-alternatives
AutoML Tables enables data teams to automatically build and deploy state-of-the-art ML models on structured data at an increased speed and scale.
-
/identity-aware-proxy-alternatives
Google Cloud’s Identity-Aware Proxy implements zero-trust access for GCP resources.
-
/alarm-com-for-business-alternatives
Smarter Business Security combines intelligent IDS, video surveillance, access control, and energy management into a single solution.
-
/google-cloud-endpoints-alternatives
Google Cloud Endpoints provides the tools to develop, deploy, protect and monitor your APIs.
-
/apereo-cas-alternatives
CAS provides enterprise single sign-on service for the web.
-
/google-security-scanner-alternatives
Allows developers to scan their apps for vulnerabilities
-
/shibboleth-alternatives
standards based, open source software for web single sign-on across or within organizational...
-
/data-loss-prevention-api-alternatives
Cloud DLP enables developers and data owners to better understand and manage sensitive data.