Vulners API
Vulnerability database enriched with millions CVE, exploits, articles, varied tools and services for vulnerability management against cybersecurity threats
Vulners API Alternatives
The best Vulners API alternatives based on verified products, community votes, reviews and other factors.
Latest update:
-
/nessus-alternatives
Nessus Professional is a security platform designed for businesses who want to protect the security of themselves, their clients, and their customers.
-
/pentest-tools-alternatives
Pentest-Tools.com is your ready-to-use setup for security testing
-
Try for free
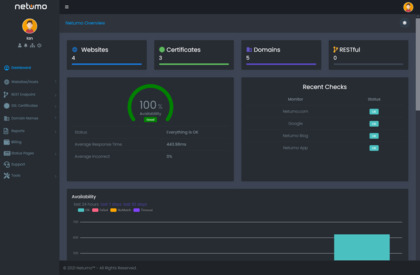
Ensure healthy website performance, uptime, and free from vulnerabilities. Automatic checks for SSL Certificates, domains and monitor issues with your websites all from one console and get instant notifications on any issues.
-
/probe-ly-alternatives
Intuitive and easy-to-use webapp vulnerability scanner
-
/metasploit-alternatives
Find security issues, verify vulnerability mitigations & manage security assessments with Metasploit. Get the world's best penetration testing software now.
-
/openvas-alternatives
The Open Vulnerability Assessment System (OpenVAS) is a framework of several services and tools...
-
/shodan-alternatives
Shodan is the world's first search engine for Internet-connected devices.
-
/paladinvpn-alternatives
PaladinVPN is one of the best virtual private network services to protect all data you receive or send over the internet.
-
/phonesploit-pro-alternatives
An all-in-one hacking tool to remotely exploit Android devices using ADB and Metasploit-Framework to get a Meterpreter session.
-
/mimikatz-alternatives
It's well known to extract plaintexts passwords, hash, PIN code and kerberos tickets from memory. mimikatz can also perform pass-the-hash, pass-the-ticket, build Golden tickets, play with certificates or private keys, vault... maybe make coffee?
-
/snyk-alternatives
Snyk helps you use open source and stay secure. Continuously find and fix vulnerabilities for npm, Maven, NuGet, RubyGems, PyPI and much more.
-
/acunetix-alternatives
Audit your website security and web applications for SQL injection, Cross site scripting and other...
-
/hostedscan-alternatives
Online vulnerability scanner for servers, networks, and web applications.
-
/fofa-alternatives
FOFA is a Search Engine for global cyberspace mapping. Through continuous active detection of global Internet assets, identifying most software and hardware network assets.
Vulners API discussion