TruSTAR
TruSTAR is a threat intelligence exchange platform built to protect and incentivize information sharing. subtitle
TruSTAR Alternatives
The best TruSTAR alternatives based on verified products, community votes, reviews and other factors.
-
/hackerone-alternatives
HackerOne provides a platform designed to streamline vulnerability coordination and bug bounty program by enlisting hackers.
-
/acunetix-alternatives
Audit your website security and web applications for SQL injection, Cross site scripting and other...
-
Try for free
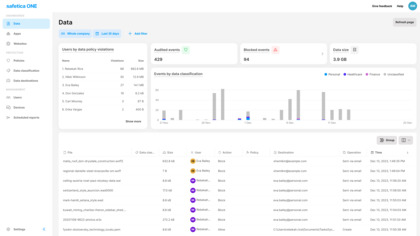
We believe data protection should make running your business easier, not harder. Safetica protects companies against insider threats, offers data loss protection, and supports regulatory compliance.
-
/trustwave-services-alternatives
Trustwave is a leading cybersecurity and managed security services provider that helps businesses fight cybercrime, protect data and reduce security risk.
-
/forcepoint-web-security-suite-alternatives
Internet Security
-
/bae-systems-cyber-security-alternatives
Bae Systems Cyber Security provides cyber intelligence and security solutions to government agencies.
-
/varonis-alternatives
Varonis is a pioneer in data security and analytics, fighting a different battle than conventional cybersecurity companies.
-
/change-tracker-enterprise-alternatives
NNT Change Tracker uses either an agent-based or agentless architecture and scans the devices and compares them to a standard policy.
-
/opswat-alternatives
OPSWAT offers an advanced threat detection and prevention platform.
-
/recorded-future-alternatives
Recorded Future provides organizations with real-time threat intelligence.
-
/dnsfilter-alternatives
DNSFilter offers DNS-Based Content Filtering & Threat Protection.
-
/dtex-alternatives
Dtex is a cyber security solution provider.
-
/vipre-threat-iq-alternatives
Threat IQ is the up-to-the-minute threat intelligence most enterprises lack that gives access to a constant stream of malicious URLs and IP addresses, suspected malicious files, phishing links and other malware data processed by labs.
-
/alert-logic-threat-manager-alternatives
Alert Logic Threat Manager is a cloud-based managed intrusion detection and vulnerability assessment solution.