Leakwatch
We keep an eye on the web to detect your data leaks in real time and enable you to take actions... subtitle
Leakwatch Alternatives [Page 3]
The best Leakwatch alternatives based on verified products, community votes, reviews and other factors.
Latest update:
-
/breachdirectory-org-alternatives
BreachDirectory.org allows you to search through all public data breaches to make sure your emails, usernames, passwords, and domains haven't been compromised.
-
/aptible-alternatives
Aptible is a secure, private cloud deployment platform built to automate HIPAA compliance.
-
Try for free
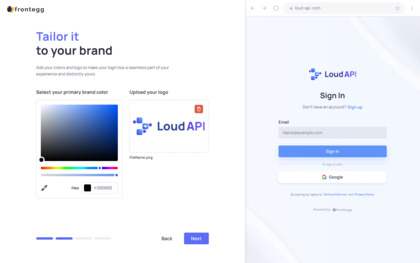
Elegant user management, tailor-made for B2B SaaS
-
/stealthaudit-management-platform-alternatives
STEALTHbits Technologies is a leader in the Microsoft Infrastructure and Application Management space, with solutions for Data Access Governance, Identity Access Management, Active Directory, and more.
-
/sophos-safeguard-encryption-alternatives
Centrally managed full-disk and file encryption with options to synchronize with award winning Sophos endpoint protection for automated, proactive data protection.
-
/symantec-cloudsoc-casb-gateway-alternatives
Symantec CloudSOC Cloud Access Security Broker (CASB) is the broadest, deepest protection for the public cloud: visibility, data security, and threat protection for SaaS, PaaS, and IaaS.
-
/netwrix-auditor-alternatives
Configuration Auditing of IT Infrastructure
-
/azure-information-protection-alternatives
An technical overview of the Azure Information Protection service, which helps an organization label documents and emails to classify and protect its data, wherever it resides.
-
/varonis-alternatives
Varonis is a pioneer in data security and analytics, fighting a different battle than conventional cybersecurity companies.
-
/symantec-information-centric-tagging-alternatives
Symantec's Data Classification offering empowers users to protect sensitive data by applying classification as they create it.
-
/fileaudit-alternatives
FileAudit monitors, archives and reports on access (or access attempts) to sensitive files and folders stored on Microsoft Windows systems.
-
/scattered-secrets-alternatives
Find out if your passwords are hacked ⚠️
-
/stealthintercept-alternatives
STEALTHbits Technologies is a leader in the Microsoft Infrastructure and Application Management space, with solutions for Data Access Governance, Identity Access Management, Active Directory, and more.
-
/ibm-data-risk-manager-alternatives
IBM Data Risk Manager, formerly known as Agile 3 Solutions, empowers C-suite executives the ability to assess risks through a dynamic data risk control center.